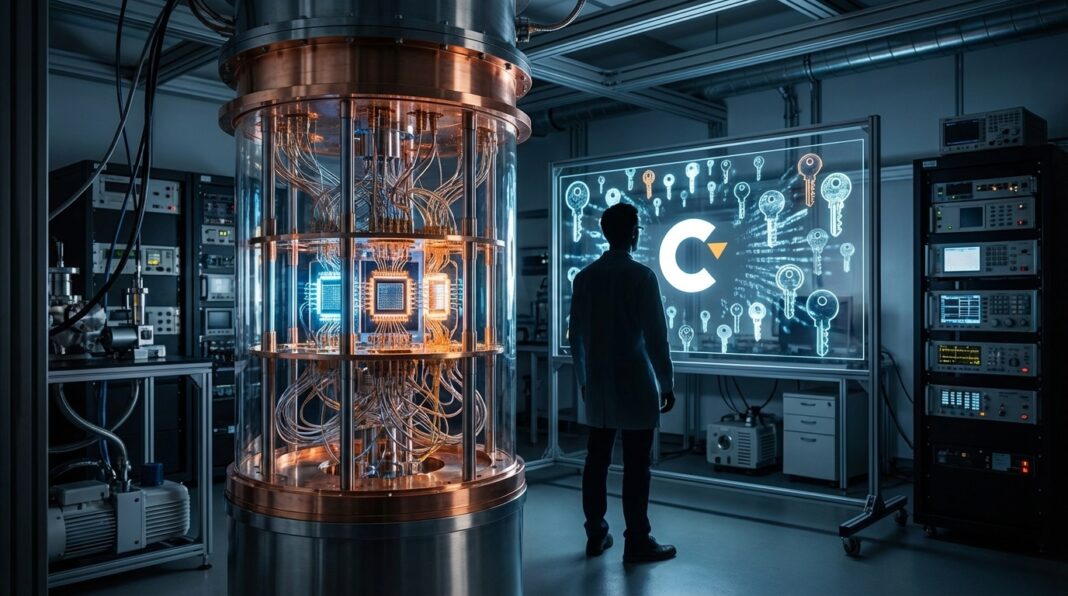
Google’s recent findings indicate quantum computing could break Bitcoin’s cryptography sooner than expected, estimating that cracking Bitcoin and Ethereum could require fewer than 500,000 physical qubits and giving two attack methods each needing about 1,200 to 1,450 high-quality qubits. Google identified 2029 as a milestone for useful quantum systems and urged migration before then. Because public keys are briefly revealed during sends, a fast quantum computer could derive private keys and redirect funds in real time.
Google designed two potential quantum attack methods aimed at the cryptography used by Bitcoin and Ethereum. Each of those two methods is estimated to require roughly between 1,200 and 1,450 high-quality qubits to carry out the described attack procedures. The source specifies those qubit ranges as the resource requirements associated with each attack method rather than presenting a single combined qubit total. The descriptions treat the two methods as separate options and assign the stated high-quality qubit ranges to each one.
Separately, Google estimated that cracking the cryptography used by Bitcoin and Ethereum could require fewer than 500,000 physical qubits. That physical-qubit estimate is presented in addition to the high-quality qubit figures given for the two individual attack methods. Those numerical figures are the specific qubit requirements provided in the source material.
When someone sends bitcoin, a public key is briefly revealed. A fast enough quantum computer could use that information to calculate the private key and redirect the funds. An attack could target transactions in real time rather than old wallets. The brief exposure of public keys during sends is the mechanism described in the source that enables a quantum-assisted attacker to attempt immediate key recovery and transaction interception.
In contrast to attacks against dormant wallets, the source highlights the possibility of executing quantum attacks at the moment of transfer when public keys appear. The distinction between real-time transaction attacks and retroactive wallet compromises is stated explicitly in the source. Those points are presented as the specific transactional vulnerability and the cited difference in attack timing in the source material clearly.
Google’s recent analysis frames advancing quantum computing as a technical challenge to current cryptographic protections for Bitcoin and similar systems, and it ties that challenge to a specific timeline marked by a 2029 milestone that is presented as a deadline for migration planning.
Google states migration to quantum-resistant systems needs to occur before the 2029 milestone, and it links the timeline to technical constraints identified in the analysis.